Rumba Ransomware Decryptor
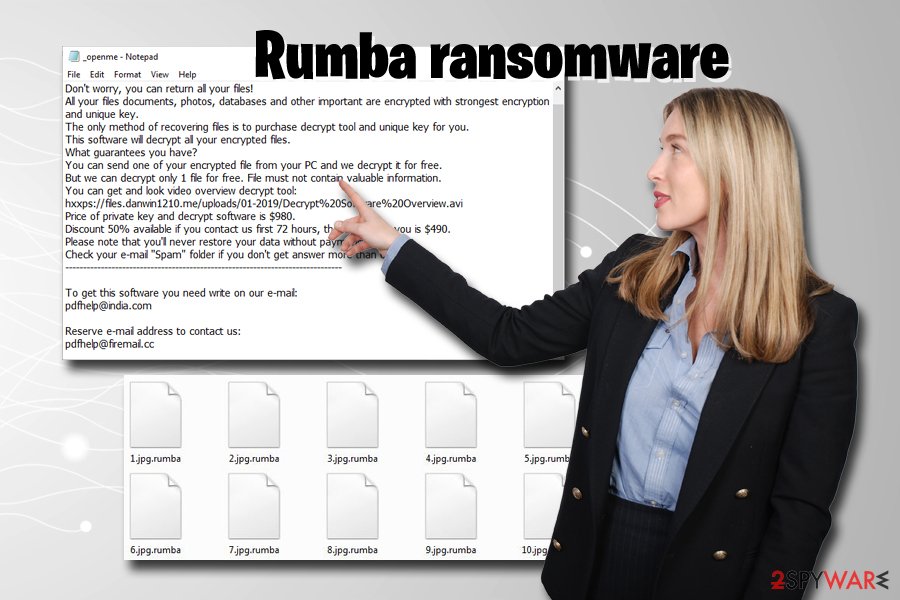
What is Rumba ransomware
Once you get remove Rumba ransomware, you can try one of three options to recover your data: use a decryptor created by experts, use backups, or make use of third-party recovery software. We are convinced that one of the methods should work for you, so check the guide below. The.Rumba Ransomware is a malware which created in order to encrypt photos, documents and music. It hijack a whole personal computer or its data and demand a ransom in order to unlock (decrypt) them. The developers of the.Rumba ransomware virus have a strong financial motive to infect as many computers as possible.
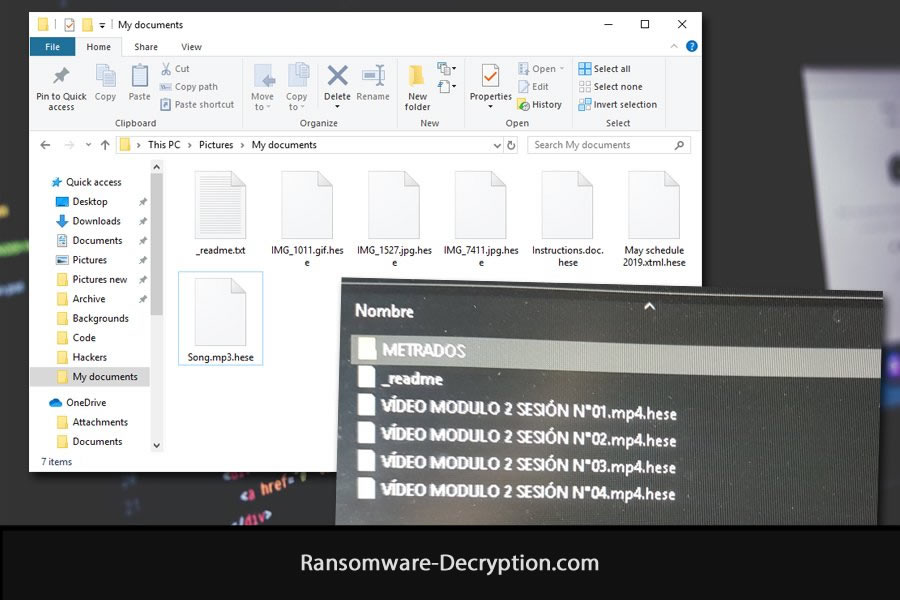
Rumba is one of the newest variants of Djvu (STOP) ransomware. Most of the time users get this ransomware onto their computers after downloading software cracks. After getting into the system, Rumba encrypts most files on the computer and upends .rumba extension to them. Rumba leaves ransom notes called _openme.txt in folders with encrypted files. Rumba might also change the hosts.txt file (located in C:WindowsSystem32driversetc folder) on the infected machine: add known sites about computer security and antivirus sites to the list of domains the computer is forbidden from connecting to. Meaning: users won’t be able to access sites they need to get rid of the ransomware. Rumba might create a scheduled task to launch its encryptor at random intervals, to encrypt new files that have been created after the initial infection or files that have been restored from backup.
While some of the earlier variants of STOP ransomware can be decrypted with a free decryptor tool created by security researches, that decryptor cannot decrypt .rumba files at the time of writing.
Update: you may try your chances with STOPDecrypter by Michael Gillespie (Demonslay335).
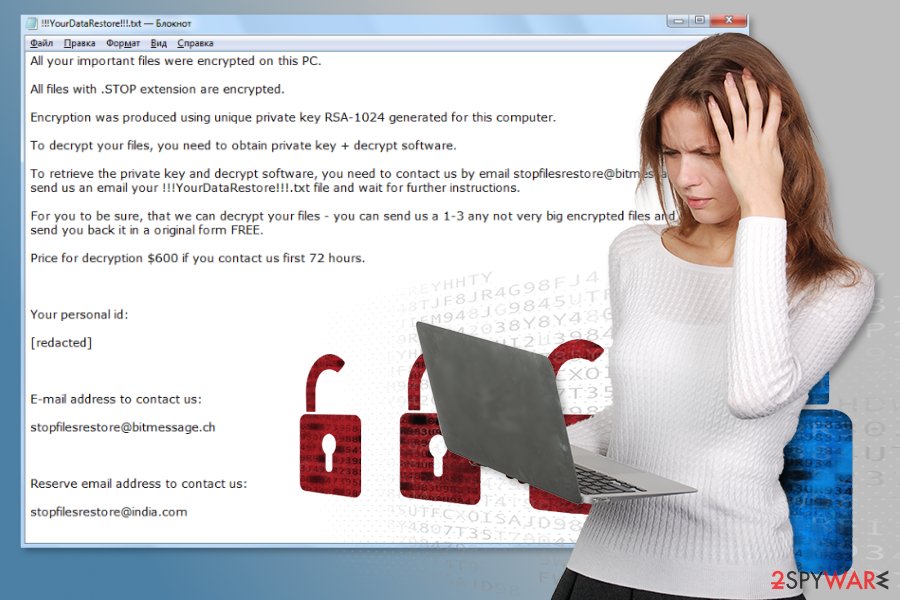
Text of the ransom note (_openme.txt)
—————————– ALL YOUR FILES ARE ENCRYPTED ———————————————–
Don’t worry, you can return all your files!
All your files documents, photos, databases and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://files.danwin1210.me/uploads/01-2019/Decrypt%20Software%20Overview.avi
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” folder if you don’t get answer more than 6 hours.
—————————————————————————————————————————
To get this software you need write on our e-mail:
pdfhelp@india.com
Reserve e-mail address to contact us:
pdfhelp@firemail.cc
Your personal ID:

How to Remove Rumba Ransomware
If you have working backups of your encrypted files or you are not going to try and recover lost files, then scan your computer with one or several antivirus and anti-malware programs or reinstall the operating system altogether.
Some alternatives:
Malwarebytes (Windows, macOS & Android)
How to Recover Files Encrypted by Rumba Ransomware
If you want to recover files encrypted by ransomware you can either try to decrypt them or use methods of file recovery.
Ways to decrypt the files:
Rumba Ransomware Decryptor Tool
- Contact the ransomware authors, pay the ransom and possibly get the decryptor from them. This is not reliable: they might not send you the decryptor at all, or it might be poorly done and fail to decrypt your files.
- Wait for security researchers to find some vulnerability in the ransomware that would allow you to decrypt files without paying. This turn of events is possible but not very probable: out of thousands of known ransomware variants only dozens were found to be decryptable for free. You can visit NoMoreRansom site from time to time to see if free decryptor for ransom1 exists.
- Use paid services for decryption. For example, antivirus vendor Dr. Web offers its own decryption services. They are free for users of Dr.Web Security Space and some other Dr. Web’s products if Dr. Web have been installed and running at the time of encryption (more detail). For users of other antiviruses the decryption, if it’s deemed possible, will cost €150. According to Dr. Web’s statistics, the probability of them being able to restore files is roughly 10%.
Other ways to recover encrypted files:
Rumba Ransomware Decryptor 2
- Restore from backup. If you make regular backups to a separate device and check from time to time that those are in working order and files can be successfully restored – well, you probably won’t have any problems getting back your files. Just scan your computer with a couple of AVs and anti-malware programs or reinstall operating system, and then restore from backup.
- Recover some files from cloud storage (DropBox, Google Drive, OneDrive, etc.) if you have one connected. Even if encrypted files were already synced to the cloud, a lot of cloud services keep old versions of altered files for some time (usually 30 days).
- Recover Shadow Volume Copies of your files if those are available – ransomware usually tries to delete them too. Volume Shadow Copy Service (VSS) is a Windows technology that periodically creates snapshots of your files and allows you to roll back changes made on those files or recover deleted files. VSS is enabled together with System Restore: it’s turned on by default on Windows XP to Windows 8 and disabled by default on Windows 10.
- Use file recovery software. This probably won’t work for Solid State Drives (SSD – it is a newer, faster and more expensive type of data-storage devices) but is worth a try if you store your data on a Hard Disc Drive (HDD – older and more common as of yet storage device). When you delete a file from your computer – and I mean completely delete: use Shift + Del or empty the Recycle Bin – on SSD it gets wiped from the drive right away. On HDD however, it rather gets marked as deleted, and the space it occupies on a hard drive – as available for writing, but the data is still there and usually recoverable by special software. However, the more you use the computer, especially if you do something that writes new data on the hard drive, the more chance that your deleted file gets overwritten and will be gone for good. That is why, in this guide we will try to recover deleted files (as you remember, ransomware creates an encrypted copy of a file and deletes the original file) without installing anything on a disk. Just know that this still might not be enough to successfully recover your files – after all, when ransomware creates encrypted files it writes new information on a disk, possibly on top of files it just deleted. This actually depends on how much free space is there on your hard drive: the more free space, the less chance that new data will overwrite the old data.
- This might void your warranty.
- It’s harder to do with laptops, and you’ll need a special case (disk enclosure) to put a hard drive in before connecting it to another machine.
- It is possible to infect the other computer if you open a file from the infected drive before scanning the drive with AVs and removing all found malware; or if all AVs fail to find and delete the malware.
- Restart the computer.
- Once you see a boot screen tap F8 key continuously until a list of options appears.
- Using arrow keys, select Safe Mode with Networking.
- Press Enter.
- Hold down Windows key and hit X key.
- Select Shut down or sign out.
- Press Shift key and click on Restart.
- When asked to choose an option, click on Advanced options =>Startup Settings.
- Click Restart in the bottom right corner.
- After Windows reboots and offers you a list of options, press F5 to select Enable Safe Mode with Networking.
- Launch Shadow Explorer.
- On the top left part of the window you can select a disk (C:, D:, etc.) and a date when a snapshot of files was taken.
- To recover a file or a folder right-click on it and select Export….
- Choose where do you want to put the files.
Going further, we need to 1) stop ransomware from encrypting files that we recover, if malware is still active; 2) try not to overwrite files deleted by ransomware. The best way to do it is disconnect your hard drive and connect it to another computer. You will be able to browse all your folders, scan them with antivirus programs, use file recovery software or restore data from Shadow Volume Copies. Although it is better to download all tools you’ll need beforehand and disconnect the computer from the Internet before connecting the infected hard drive, just to be safe.
Disadvantages of this method:
Another, easier, way is to load into Safe Mode and do all file recovery measures from there. However, that will mean using the hard drive and potentially overwriting some data. In this case it’s preferable to use only portable versions of recovery software (the ones that don’t require installation), download them onto an external device, and save any recovered files onto an external device too (external hard drive, thumb drive, CD, DVD, etc.).
Boot Into Safe Mode:
Windows XP, Windows Vista, Windows 7:
Windows 8, Windows 8.1, Windows 10:
Back up Your Encrypted Files
It is alwayse advisable to create a copy of the encrypted files and put it away. That might help you if free ransomware decryptor becomes available in the future, or if you decide to pay and get the decryptor but something goes wrong and files get irreparably damaged in the process of decryption.
Use File Recovery Tools to Recover Files
Screenshot:
About Stellar Data Recovery
R-Undelete
How to recover deleted files with R-Undelete
Puran File Recovery
Video guide on how to use Puran File Recovery
Recover Encrypted Files From Shadow Copies.
The easiest way to access Shadow Volume Copies is by using a free tool called Shadow Explorer. Just download the latest version and install it (or download the portable version).
Remove Rumba Ransomware
Now that you have your recovered or still encrypted files on an external device, it is time to scan your computer with AV and anti-malware software or, better yet, reinstall the operating system, to fully get rid of possible ransomware traces. Remember to also scan your external device before putting files back on your computer!